20 February 2009 - 8:09Who Are You? Stop Asking Me!
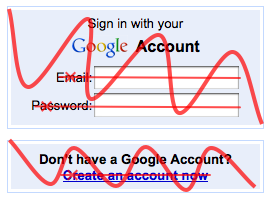
Are you asked to sign-in to websites often? “Remember me” doesn’t seem to always work..
Do you have many user names? At least sites let you use your email address nowadays..
Have you forgotten your password? Saved by password manager..?
Is your password hard to hack? But I’m too lazy to make/remember a stronger password…

Google's account troubleshooter
Why do websites have sign-in forms anyway?
I suppose the site just wants to ask “who are You?” Signing in lets you personalize your experience on the site. Let You get to the stuff You want. That’s just some of the benefits for the user.
For the website, it wants to make sure it only gives your stuff to you and not some random person that’s also using the site. One way to ensure that is to “challenge” you by making you answer something that hopefully only you know.. like your username and password.
But what if the browser you’re using already knows that you are You?
Instead of challenging You to see if you happen to remember your username and password, the website could challenge your browser to prove that it’s You. Now you don’t need to worry about forgetting your password or username. You don’t need to worry about having a weak password either because computers are good at remembering and calculating complex stuff.
But that’s not all! One very useful aspect is that you wouldn’t even need to sign in to websites anymore!
The challenges that site asks to prove that you’re You can be made in a way that only your web client can answer them. So when you go back to the website, it already knows who you are, and nobody else can pretend to be you. And this is only if you let your client tell the site.
Even better is that you don’t even need to create an account on the website! 🙂
You can start using and personalizing your experience on a site without first going through the user creation process. Because the site knows that only you can be You, you can focus on getting a better experience now and later go through the nitty gritty details of providing a name, contact information, etc. if necessary.
Use the site first, create an account later
For example, if you’re using a site to purchase items, e.g., stuff for a house or even a house, you could make notes on items without first creating an account. Next time you visit, the site already knows it’s You, and this is without being required to put any personal information. The site might eventually want your email address to send you notification that this item just got cheaper by 50%, but that’s up to you.
But what about privacy?
Just because one site knows you’re You doesn’t mean another site can know that. You could choose which sites your browser accepts these identification challenges, and if it doesn’t respond, the site can’t figure out who you are any better than how things are now.
Additionally, because computers are good at doing menial things like tracking lots of numbers, the way it answers challenges can be different for each site. So if you took a bad approach to this problem by just having the web client make some identification number, the web client could give a different identification number to each site instead of sharing the same number. That’s just to get a crude feel of how a client can maintain your privacy across sites, but real implementations would have much more complex challenges.
Go Phish?
If you happen to stumble upon a phishing site that didn’t automatically get blocked, there’s a lot more red flags that will be going off for the user. “Why do I need to all of a sudden sign into this site?” “Uhh.. how do I even sign in.. my client handles all that for me..” 😉
If all this was part of a cloud-based web client like EdBrowser, you can get this great experience no matter where you go. As long as you first get your information from the cloud to the client you’re using, your client will have enough information to answer the challenges to prove that you’re You, even if you’re at another computer like a mobile device.
The EdBrowser first simplifies Going Places by getting you there in a single click, and now you can make use of websites without needing to type in a username/email and password! There’s fewer and fewer reasons to touch the keyboard just to get to your actual goal — to use the site!
10 Comments | Tags: EdBrowser, Mozilla
Sounds like OpenID (unfortunately, since it never took off) except it requires browser support.
Right. There are a number of solutions to a single login/authentication. I didn’t really talk about how all this login stuff is done under the hood. It could very well be implemented with one of these kinds of OpenID proposals.
This is more of a brainstorming of what would happen if Identity became first-class in the browser. What better user experiences are possible when the user doesn’t need to worry about signing in?
I see a couple of issues with this general idea; I’m sure you’ve considered them, so I’d be interested to know what solutions you have in mind.
First, when will users authenticate themselves to the browser? I’d think it would have to be at least once per browser launch, since the alternative is to essentially leave the keys to your email inbox, bank accounts, etc. lying around for anyone to use. But entering a password every time the browser launches is a real pain, especially if you’re just popping online to check the weather. On the other hand, something like “require a password the first time your identity is required per session” would lead to an inconsistent user experience: “Why does Citibank only sometimes ask me to type my password?” (There’s also an issue with leaving such a powerful identity proxy up and running if you leave the browser up when you leave the room.)
And second, I’d be paranoid about vendor lock-in. Let’s say I’m one of millions of happy EdBrowser users: my accounts at Yahoo mail and Facebook and WookieFans.net are all configured with strong passwords stored inside the browser. But then you suddenly start charging EdBrowser users $1500 per year (or I buy a new computer running the revolutionary Finux OS and EdBrowser isn’t available for that platform). How do I regain access to my accounts if I switch to Google Chrome?
Sounds like the personal certificates thing browsers actually have supported for quite a while. Already a standard, portable (or at least, tools exist) between platforms / browsers. No UI in Firefox to choose what certificate to use, though 🙁 It just chooses things until it works.
Agreeing with Steuard that the whole adding the relevant key part is hard to deal with. The current master password prompt is also… not so nice.
> when will users authenticate themselves to the browser?
So before the user has access to his/her history, bookmarks, etc. s/he would need to log-into their cloud-identity just like logging into an OS. Or if you choose not to log out, it would stay logged in and have easy access to stuff.
> leave keys lying around for anyone to use
So I talked mostly about simple user account stuff like forums, but if a site has information that should be more restricted, e.g., mail and bank, the site could ask your web client for “elevated” privileges. This could be similar to how Amazon.com lets you browse their site while showing personalized information, but once you want to order something or access your account, you need to re-enter your password. And these elevated privileges could be revoked automatically after some amount of time.
> I’d be paranoid about vendor lock-in.
Ideally it’s an open solution. 🙂 But even before that, the goal is for *you* to be in charge of your information. For example, you could access your cloud-account (which you put on whatever server you want) and locally (client-side JS) decrypt your personal information. From there potentially there could be an alternative/traditional login/password. These could still be strong passwords, but that’s fine because you could be using IE and copy/paste this crazy-long username and password. (User experience there could probably be better…)
But this just got me thinking about security problems with browsers and untrusted add-ons. Once you locally decrypt your information, an add-on could easily grab that information… Hrmm…
Well, my take on making authentication easy has always involved email (or instant messaging) callbacks.
I’ve noticed that almost everyone uses the “Forget Password” feature all the time when it’s available. Why not make it the primary login system?
e.g. To sign up to a site, ALL you have to do is put in your email address (and verify it the way it’s done today). To sign in, you’d put in your email address, get an email back with a temporary login link, and then use it to login.
Of course, this is too slow. But if some kind of messaging system were integrated into the browser, this would remove the associated delays.
The nice thing about this is that you have control over how many passwords you use. You might be happy with just one (the one you use for your email). Or you might create 2 email addresses, one for business logins, one for personal logins.
The killer advantage? Phishing is impossible… (well, the usual sort).
> Sounds like the personal certificates thing browsers actually have supported
I’m not totally familiar with these personal certs, but doesn’t the user have to get a cert somehow?
Part of what I’m describing is based on how you can have password-less login through SSH if you have a public/private key. So potentially you could give your public key to a site, and it can figure out that you really do have your private key.
The key aspect about all this though is that this identifying information is bound to your Identity — part of your cloud-account. So if you go to another machine, you get your identity and the client will authenticate for you. Similarly, if someone else uses your machine, they should switch to their account.
Incidentally, Ed, are you suggesting something like I’ve suggested? I didn’t think that was the case at first, but now re-reading, despite some technical differences, it does sound fairly similar. Maybe I need to wait until you’ve elaborated a bit more. 🙂
Kindof. Without the whole email thing, but you did suggest something more automatic.
But basically yes.
1) The user makes a request for the site by visiting it
2) The server asks your web client to prove it’s you
3) Only your client can prove it’s you and gives proof
4) Server grants access
Instead your original suggestion was 1) user clicks “forgot my password” 2) server sends email to user 3) user logs into email and clicks link 4) user logged in
For me it is important to differentiate between the types of authentication commonly needed:
1. Weak authentication: For forums, blogs and webmail hosts the need is to link a visitor to a user record on the system. In other words, what matters to you is differentiating between the visitors while you don’t really care what their real name is. For such cases solutions like OpenID or a master password or a browser password manager combined with automatic profile fill-in should suffice.
2. Strong authentication: For online shopping, banking and government services, besides the above need, you also must know the official identity of the user, that is, their real name, address, etc.
As Mook mentioned, personal certificates is one possible solution for strong authentication. The technology and standards behind them have existed for ~ 10 years (check wikipedia for PKI / X.509) and all common browsers support them. These certificates function pretty much like the server SSL certificates, but they are issued to a person instead of a website.
A personal digital certificate is like a passport or a driving license. When a traffic policeman or a border official check your identity obviously it won’t suffice to say “Hi, I’m Ed and I know who I am” 😉 Instead they will ask you for a certificate (driving license, passport) issued by someone who they trust (not you, but a government agency).
So, for strong authentication, the website must check your identity with a trusted authority – the so called CA (certificate authority). And the question here is not “Who are you?”, but actually “Who is he?” 😉
In my country (Bulgaria) personal certificates are issued by a number of certified government agencies, banks and notaries. You present them with your ID card and pay ~ 25 Euro. In return they issue you a digital certificate, signed (digitally) by them and stored on a smart card. To access your smart card you receive a PIN. You also receive a USB card reader which you connect to your PC. To sign a document or an email, or to authenticate yourself on the web (through the browser) you put your smartcard into the reader and enter the PIN to unlock the certificate. The other party (e.g. online bank) then checks the validity of your signature with the issuing authority (CA).
Currently these personal certificates are used for things like online banking, filing your tax forms, registering a business, checking your social security status, etc.
The idea of storing your certificate on a smart card is that you can always have it with you and use it on various computers. Obviously, you should make sure that nobody else has access to the card and the PIN 🙂